#claude-code-security
#claude-code-security
[ follow ]
#cybersecurity #ai #claude-code #anthropic #vulnerabilities #ai-security #openai #security #malware #prompt-injection
fromSecurityWeek
6 days agoApple Intelligence AI Guardrails Bypassed in New Attack
The first is Neural Execs, a known prompt injection attack that uses 'gibberish' inputs to trick the AI into executing arbitrary, attacker-defined tasks. These inputs act as universal triggers that do not need to be remade for different payloads.
Apple
Artificial intelligence
fromSecurityWeek
1 month agoClaude's New AI Vulnerability Scanner Sends Cybersecurity Shares Plunging
Cybersecurity company stocks fell sharply after Anthropic announced Claude Code Security, an AI capability for finding code vulnerabilities, triggering market concerns about AI replacing traditional security solutions.
Information security
fromThe Hacker News
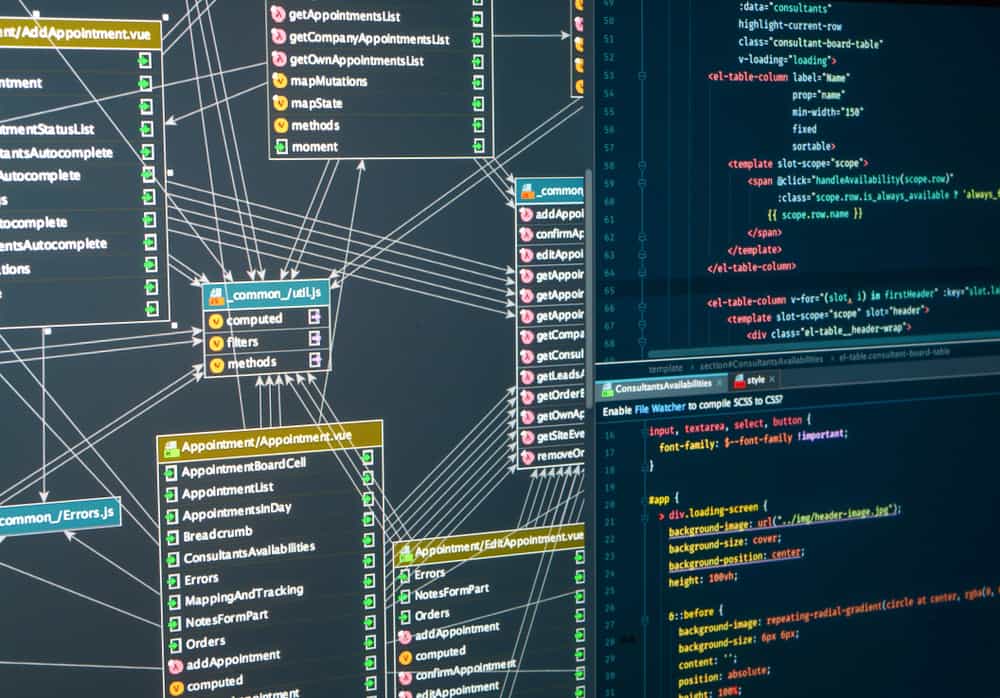
4 weeks agoClaude Code Security and Magecart: Getting the Threat Model Right
Magecart attacks hide malicious code in dynamically loaded third-party assets and EXIF metadata, bypassing repository-based static analysis tools like Claude Code Security because the code never enters the source repository.
Information security
fromTheregister
1 month agoClaude's collaboration tools allowed remote code execution
Claude Code contained three security vulnerabilities allowing remote code execution and API key theft through malicious repository configurations, posing significant supply chain risks to developers.
[ Load more ]