US politics
fromNextgov.com
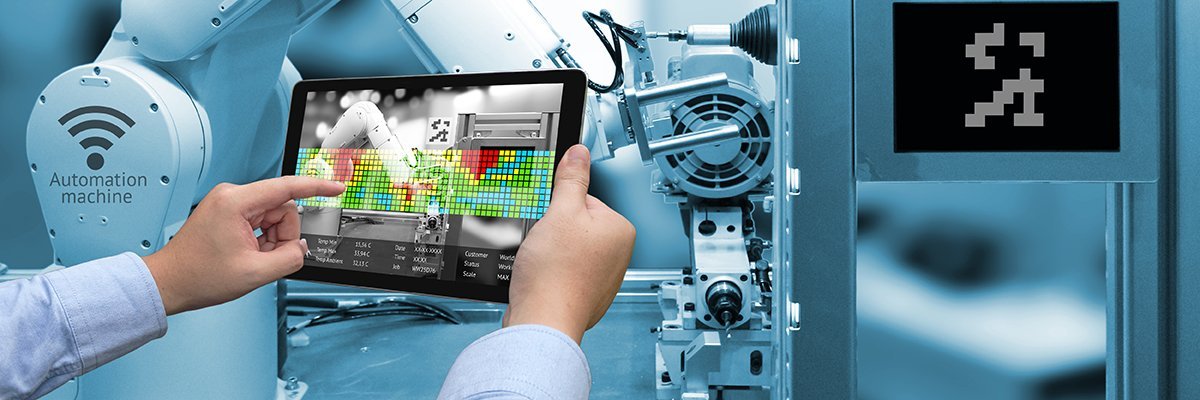
13 hours agoSecret Service is embracing new solutions to combat malicious drones, director says
The U.S. Secret Service is adopting kinetic mitigation technologies to counter drone threats for upcoming large-scale events.