#dr-dos-revival
#dr-dos-revival
[ follow ]
#cybersecurity #technology #security #linux #kernel-drivers #supply-chain-attack #cybercrime #social-engineering
fromEngadget
2 days agoA maverick hacker got Mac OS X running on a Wii
"Last year, when I saw that Windows NT had been ported to the Wii, I felt a renewed sense of motivation. Even if my lack of low-level experience resulted in failure, attempting this project would still be an opportunity to learn something new."
Games
fromThe Verge
1 week agoI saved a doomed Windows laptop by embracing Linux
The solution, according to Microsoft, is to get rid of it and buy a computer that can run Windows 11. But that's not good enough. This ThinkPad - like millions of other PCs in the same boat - is still perfectly functional.
Software development
Gadgets
fromYanko Design - Modern Industrial Design News
2 weeks ago8BitDo Retro R8 C64 Edition mouse fuses Commodore 64 nostalgia with modern gaming performance - Yanko Design
8BitDo's Retro R8 C64 Edition mouse combines nostalgic design with modern gaming features, appealing to retro gaming enthusiasts.
fromKotaku
3 weeks ago'Unhackable' Xbox One Finally Hacked, 12 Years After Release
While the PlayStation 4 was considered jailbroken by 2016, the Xbox One has remained invulnerable since its release on November 22, 2013. Well, that is until very recently, as Markus 'Doom' Gaasedelen just showcased a newly discovered 'Bliss' exploit at RE//verse 2026.
Video games
Web development
fromTheregister
3 weeks agoBrilliant backups landed web developer in big trouble
A website migration oversight caused a two-year disconnect where office staff viewed outdated content due to hardcoded DNS settings, while the client only discovered the issue when accessing the site from the office.
Privacy professionals
fromSecurityWeek
3 weeks agoHacker Conversations: Ben Harris, from Unintentional Young Hacker to Intentional Adult CEO
Ben Harris evolved from a mischievous school hacker into a legitimate cybersecurity entrepreneur, founding WatchTowr to identify and validate exploitable vulnerabilities in real-time.
fromYanko Design - Modern Industrial Design News
4 weeks agoThis Foldable DIY Cyberdeck Has Breadboards Built In and Runs Doom - Yanko Design
What separates this from a standard Raspberry Pi build is the pair of breadboards soldered directly to the GPIO pins, seated inside the case, and accessible through a removable back panel. Connecting a sensor no longer means hunting for a separate breadboard and a tangle of jumper wires. PickentCode plugged in a temperature and humidity sensor and had it reading live data within minutes.
Gadgets
fromSecurityWeek
1 month agoHacker Conversations: Inti De Ceukelaire, Raging Against the Machine Creatively
I got a rush from feeling challenged. The computer would say 'No', and I would think, 'Well, we'll see'. In his own words it was more a case of Rage Against the Machine than simply Stayin' Alive.
Digital life
fromTheregister
1 month agoDR-DOS rises again - rebuilt from scratch, not open source
The long-dormant DR-DOS.com website is alive again, and DR-DOS 9.0 is in development. There have been six preliminary releases so far this year. The current work-in-progress version is version 9.0.291. This is not the same OS as the DOS-compatible OS that Digital Research developed back in the 1980s, working on the basis of its multitasking multiuser Concurrent DOS OS.
Software development
Privacy professionals
fromFast Company
1 month agoTeenage hackers are on the rise, and they're more dangerous than you think
Teenage hackers are reshaping cybercrime through persistent, coordinated attacks that cause real harm via data breaches, feeding cycles of increasingly serious criminal activity.
fromTechRepublic
1 month agoFake Claude Code Spreads Malware to Windows, macOS Users - TechRepublic
Attackers are distributing almost identical cloned sites of popular developer tools like Claude Code with fake install instructions via malicious search engine ads - tricking victims into installing infostealer malware instead. The cloned sites closely replicate the official documentation pages for popular tools, but the installation instructions are altered to fetch malware instead of the intended software.
Information security
fromTheregister
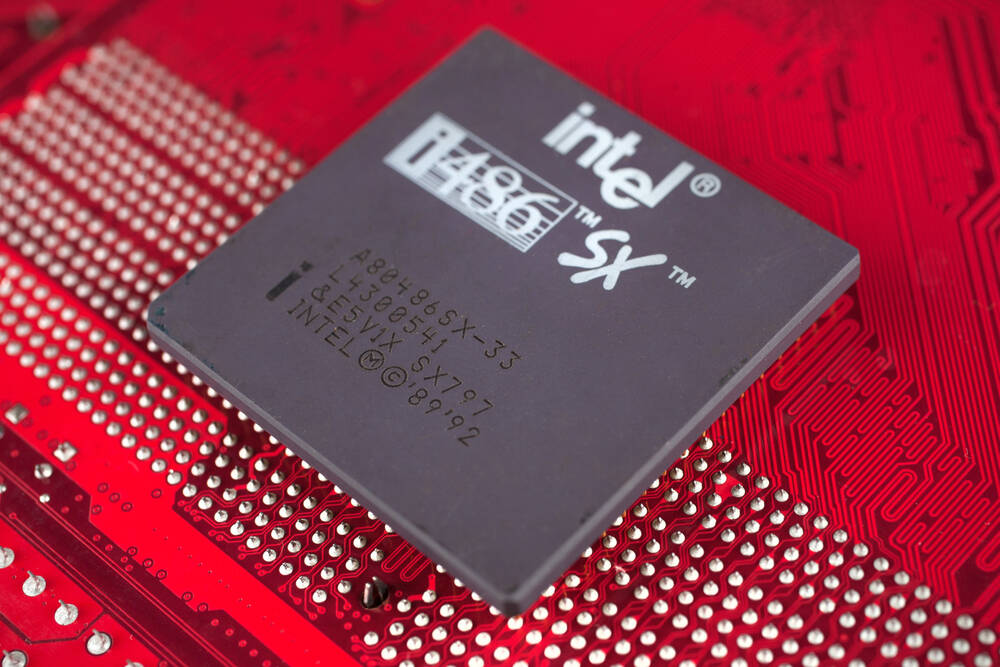
2 months agoHow CP/M-86's delay handed Microsoft the keys to the kingdom
It's the story of why the 16-bit version of Digital Research CP/M was late, but the delayed arrival of this now-obscure OS is what catalyzed the development of a different, but source-level compatible, OS. That OS started Microsoft on its way to its current $3.5 trillion capitalization, and is also what led to the development of OS/2, Windows, and indirectly Linux.
History
fromVulture
2 months agoObex Will Make You Nostalgic for Old Technology
What telling people to touch grass ignores, in part, is that grass is not all that good to touch. It's itchy and sticky - there could be bugs in there. There's a far more profoundjoyin touching machines, as is shown again and again in Albert Birney's Obex, which functions as both a shrine to and warning about our reliance on technology.
Film
fromTheregister
1 month agoReviving a CIDCO MailStation - the last Z80 computer
Pleban's talk, "Hacking the last Z80 computer ever made," was more than just a dive into retro computing. It also explored some of the many strange decisions involved in launching a new range of hardware based on the eight-bit Zilog Z80 chip in 1999 - when the 16-bit computer era was largely over, and just a couple of years before 32-bit x86 chips would be replaced by x86-64.
Gadgets
Privacy technologies
fromThe Hacker News
2 months agoMicrosoft Warns Python Infostealers Target macOS via Fake Ads and Installers
Information-stealing attacks are expanding to macOS, leveraging cross-platform languages, social-engineering lures, and trusted platforms to distribute Python-based stealers at scale.
fromKotaku
2 months agoEvery Old Game Deserves A 60FPS Update
Returning to old games isn't always easy. Depending on how old the game is, you might run into various problems, including unusual controls or compatibility issues. Another common point of friction you might encounter is an older game running poorly. This can make it a slog to replay some of the modern classics, even if they're just a decade or so old. So I'm happy to see Ubisoft going back and updating performance in games like Far Cry Primal and Assassin's Creed Unity.
Video games
fromwww.theguardian.com
2 months agoCommodore 64 Ultimate review it's like 1982 all over again!
The emotional hit was something I didn't expect, although perhaps I should have. The Commodore 64 Ultimate, a new version of the legendary 8-bit computer, comes in a box designed to resemble the original packaging a photo of the machine itself on a background of deep blue fading into a series of white stripes. Then when you open it, you find an uncannily accurate replica of what fans lovingly referred to as the breadbox the chunky, sloped Commodore 64, in hues of brown and beige,
Gadgets
Information security
fromSecurityWeek
1 month agoClaude Code Flaws Exposed Developer Devices to Silent Hacking
Check Point researchers discovered critical vulnerabilities in Claude Code that could enable attackers to gain unauthorized control of developer computers through malicious configuration files.
fromThe Hacker News
1 month agoThreatsDay Bulletin: Kali Linux + Claude, Chrome Crash Traps, WinRAR Flaws, LockBit & 15+ Stories
The average e-crime breakout time - the period between initial access and lateral movement onto another system - dropped to 29 minutes, a 65% increase in speed from 2024. One such intrusion undertaken by Luna Moth targeting a law firm moved from initial access to data exfiltration in four minutes.
Information security
fromWIRED
1 month agoThis Gadget Lets You Play Game Boy Games on a Laptop-If You Have the Cartridge
The Game Boy family of handheld consoles was groundbreaking, making gaming more accessible to millions worldwide. Nintendo's portables beat off technologically superior competition from the likes of Sega's Game Gear and Atari's Lynx. They became home to foundational moments for the medium, from what is still arguably the definitive version of Tetris to the birth of Pokémon. Yet with the iconic gray monolith launching in 1989, it's now pushing 40-and playing those important classics gets tougher every year.
Gadgets
fromZDNET
1 month ago8 Linux distros I always recommend first to developers - and why
For the longest time, Linux was considered to be geared specifically for developers and computer scientists. Modern distributions are far more general purpose now -- but that doesn't mean there aren't certain distros that are also ideal platforms for developers. What makes a distribution right for developers? Although I consider app compatibility, stability, and flexibility to be essential attributes for most any Linux distribution, developers also need the right tools
Software development
fromEngadget
1 month agoHacker used Anthropic's Claude chatbot to attack multiple government agencies in Mexico
In total, it produced thousands of detailed reports that included ready-to-execute plans, telling the human operator exactly which internal targets to attack next and what credentials to use. This started in December and continued for around a month, resulting in the theft of 150GB of official government data, including taxpayer records, employee credentials and more.
Information security
fromTheregister
2 months agoOld Windows quirks help punch through new admin defenses
The issue focuses on how Windows handles these directories for specific user sessions. Because the kernel creates a DOS device object directory on demand, rather than at login, it cannot check whether the user is an admin during the creation process. Unlike UAC, Administrator Protection uses a hidden shadow admin account whose token handle can be returned by the system when calling the NtQueryInformationToken API function.
Information security
Information security
fromThe Hacker News
2 months agoThreatsDay Bulletin: New RCEs, Darknet Busts, Kernel Bugs & 25+ More Stories
Small, quiet shifts across systems—abused trusted tools and unnoticed vulnerabilities—are causing privilege escalation, cryptomining infections, and broader erosion of access, data, and trust.
fromTheregister
2 months agoMicrosoft finally ends extended updates for ancient Windows
January 13 marked another milestone for legacy systems, as support for the software - codenamed Longhorn Server - expired for customers that bought Microsoft Premium Assurance (PA). Extended support ended for Windows Server 2008 on January 14, 2020. It was possible to keep the lights on until January 10, 2023, via Extended Security Updates. A fourth year came courtesy of Azure, which took the code to January 9, 2024, but that was it for anyone without PA.
Information security
fromDataBreaches.Net
1 month agoNew "Kurd Hackers Forum" Focuses on Middle Eastern Data Breaches and Leaks - DataBreaches.Net
Reza abasi notes that there is a new forum called the "Kurd Hacker Forum" that focuses on databreaches in Iran, Syria, and Turkey. The domain was registered January 28, 2026. The forum, which is on the clear net, looks like it has the same format as the classic BreachForums, with the same types of sections and subsections. The threads in the forum are either in English or Kurdish languages.
Information security
Information security
fromwww.theguardian.com
2 months agoI'm a tech-savvy zillennial who knows how to safeguard against hacking. Scammers still managed to get me | Caitlin Cassidy
Tech-savvy individuals can be deceived by realistic phishing while distracted, enabling scammers to steal funds through fake sites and cardless cash authorisations.
[ Load more ]