#holographic-id-cards
#holographic-id-cards
[ follow ]
#privacy #cybersecurity #facial-recognition #meta #ai #digital-identity #data-privacy #smart-glasses #security
fromwww.bbc.com
3 hours agoBiometric checks to be rolled out in prisons after mistaken releases
The findings of an independent review criticized recent mistaken releases as 'simply one symptom of a broken system.' The review was commissioned after Hadush Kebatu was mistakenly freed from an Essex prison in October 2025.
UK news
fromPopular Science
4 days agoHow to stop your smart TV from tracking you
Smart TVs are capable of tracking user data, including viewing habits and app usage, which can lead to personalized advertising and content recommendations. Users may prefer to limit this tracking to protect their privacy.
Privacy technologies
Healthcare
fromNextgov.com
1 month agoCMS touts early uses of new biometric verification tools for Medicare.gov
CMS launched modern identity verification options (Login.gov, ID.me, CLEAR) on Medicare.gov, with 25% of users adopting them within five to six days and 60% of new accounts using these credentials.
#digital-id
UK politics
fromPinkNews | Latest lesbian, gay, bi and trans news | LGBTQ+ news
1 month agoDigital IDs won't require sex and gender data, government confirms
The UK government's relaunched voluntary digital ID scheme will not collect sex or gender information, addressing concerns that it could out trans people.
Privacy professionals
fromTheregister
4 weeks agoAge verification isn't sage verification inside OSes
California's Digital Age Assurance Act attempts age verification for minors but is vague, incoherent, and creates liability risks without clearly defining compliance requirements or addressing practical implementation across diverse computing devices.
Privacy technologies
fromArs Technica
4 weeks agoWorld ID wants you to put a cryptographically unique human identity behind your AI agents
World ID's Agent Kit enables AI agents to prove human authorization through iris-verified identity tokens, allowing websites to distinguish legitimate automated requests from malicious Sybil attacks.
Privacy professionals
fromWIRED
1 month agoDo You Need an Identity Protection Service for Safe Browsing?
Identity theft protection services function as insurance products offering reactive compensation for damages rather than active prevention, with coverage details and sub-benefit caps critically affecting actual protection value.
fromFast Company
1 month agoThis crypto ring certifies your digital self with real-life handshakes
Identity spoofing against older adults alone grew by 8x between 2020 and 2024, driven in part by convincing AI impersonations of friends and loved ones. It's a problem costing people in the U.S. nearly half a billion dollars a year with no end in sight.
Privacy technologies
fromFast Company
1 month agoScanning that QR code can leave you vulnerable. Here's how to protect yourself
QR codes are two-dimensional images with glyphs of various sizes that store not just numbers, but text. When scanned, your phone extracts the encoded information and can act on it. For example, QR codes often embed URLs, allowing you to scan, say, a parking meter to launch a webpage where you can pay online.
Privacy technologies
Privacy professionals
fromPinkNews | Latest lesbian, gay, bi and trans news | LGBTQ+ news
2 months agoDiscord users must complete face or ID scans by next month
Discord will require face or government ID age verification by the end of the month, restricting access to graphic or sensitive content for unverified users.
fromSilicon Canals
1 month agoThe global infrastructure of digital ID is being built right now - and nobody voted for it - Silicon Canals
What I walked through wasn't just an immigration gate. It was a node in a rapidly expanding global infrastructure of digital identity, one being constructed at extraordinary speed, across dozens of countries, by a mix of governments, multilateral organizations, and private technology vendors. The people building it believe they are solving real problems: fraud, statelessness, inefficient public services, financial exclusion.
Privacy technologies
fromWIRED
2 months agoICE and CBP's Face-Recognition App Can't Actually Verify Who People Are
Mobile Fortify, now used by United States immigration agents in towns and cities across the US, is not designed to reliably identify people in the streets and was deployed without the scrutiny that has historically governed the rollout of technologies that impact people's privacy, according to records reviewed by WIRED. The Department of Homeland Security launched Mobile Fortify in the spring of 2025 to "determine or verify" the identities of individuals stopped or detained by DHS officers during federal operations, records show.
Privacy technologies
Information security
fromSecurityWeek
2 months agoWebinar Today: Identity Under Attack - Strengthen Your Identity Defenses
Adopt an identity-first security strategy to protect sensitive data, meet compliance requirements, and balance security, user experience, and operational efficiency against identity threats.
fromFortune
2 months agoI oversee a lab where engineers try to destroy my life's work. It's the only way to prepare for quantum threats | Fortune
This happened in the early 1990s, when I was a young engineer starting an internship at one of the companies that helped create the smart card industry. I believed my card was secure. I believed the system worked. But watching strangers casually extract something that was supposed to be secret and protected was a shock. It was also the moment I realized how insecure security actually is, and the devastating impact security breaches could have on individuals, global enterprises, and governments.
Information security
fromFuturism
1 month agoNew App Detects the Radio Fingerprint of Smart Glasses and Warns You When Someone Is Using Them Nearby
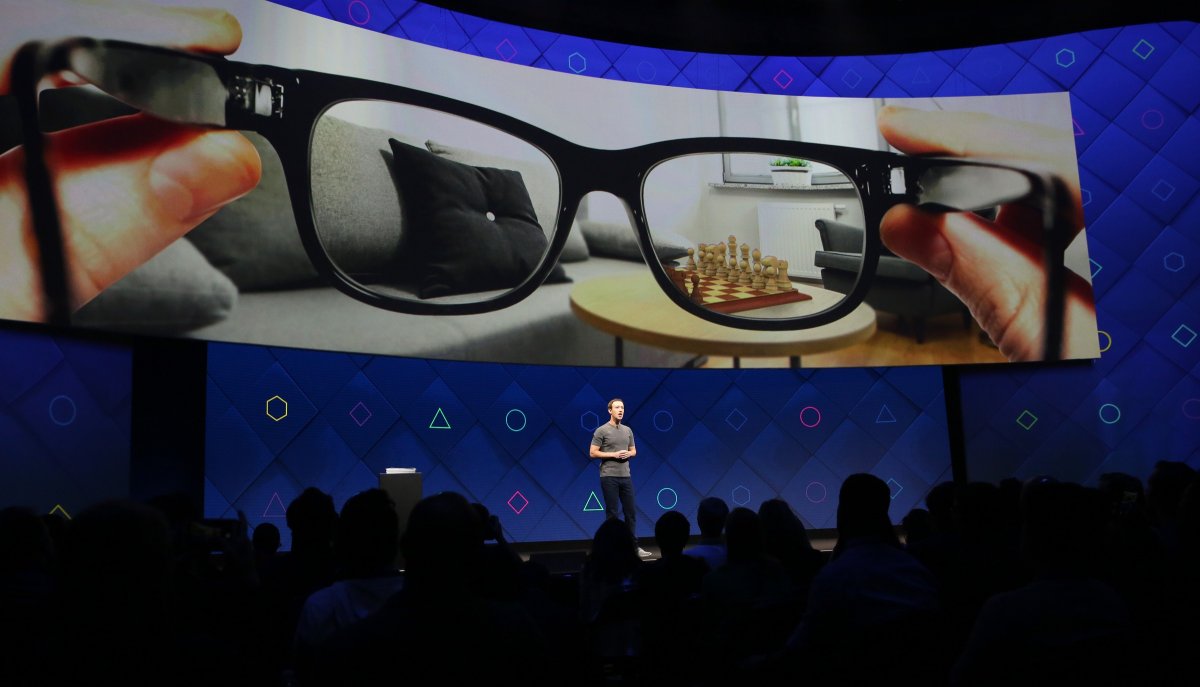
Covert recording is a lot about power. So, I was worried from the very beginning when Meta announced they were going to revive the Google Glass idea. That might be influenced by my study subject very well, but it might as well be influenced by every report and story I read on digital abuse and hate speech in the last twenty to thirty years.
Privacy technologies
[ Load more ]