#macos-credential-theft
#macos-credential-theft
[ follow ]
#cybersecurity #apple #malware #vulnerabilities #macos #vulnerability #ai #microsoft #social-engineering #ios
Careers
fromFortune
1 day agoThis CEO pirated video games as a teen and became a hacker for the Air Force. Now he's built a $3 billion cyber firm | Fortune
Gen Z should trust instincts in career paths, as demonstrated by Kyle Hanslovan's unconventional journey to CEO of a $3 billion cybersecurity firm.
fromwww.socialmediatoday.com
2 days agoGrok faced potential removal from the App Store
Apple privately threatened to remove Elon Musk's artificial intelligence app, Grok, from its App Store in January after Musk's xAI failed to do enough to stop it from creating nude or sexualized deepfakes.
Artificial intelligence
#ai
Information security
fromFortune
4 days agoAnthropic caused panic that Mythos will expose cybersecurity weak spots, but one industry veteran says real problem is fixing, not finding, them | Fortune
Anthropic's Claude Mythos Preview AI model identifies cybersecurity vulnerabilities, but experts question its impact on fixing existing issues.
#iphone-security
Information security
fromArs Technica
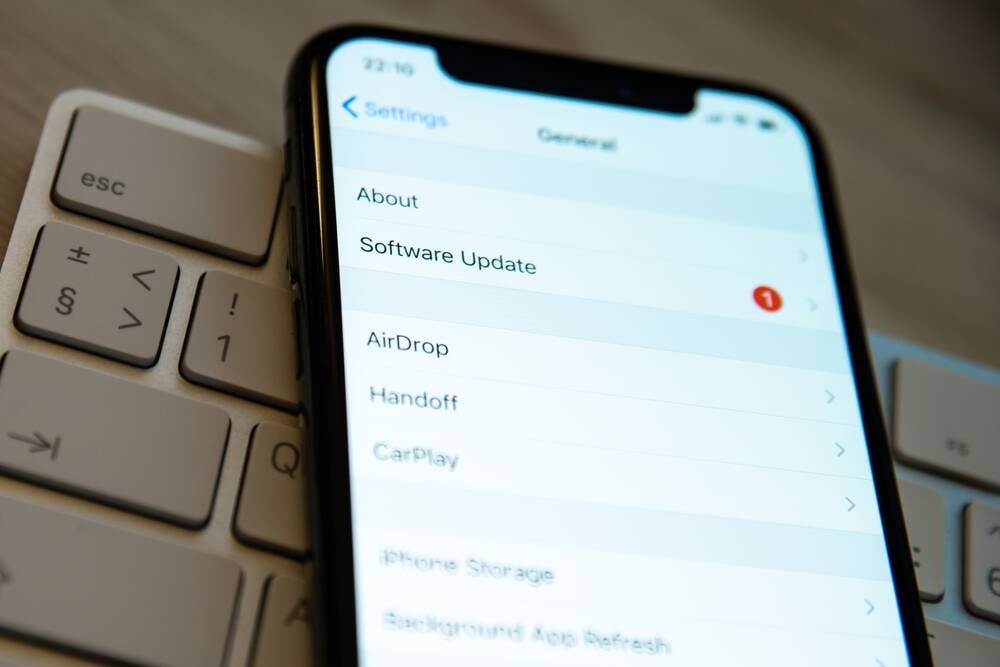
4 weeks agoHundreds of millions of iPhones can be hacked with a new tool found in the wild
DarkSword, a sophisticated iPhone hacking technique discovered in use by Russian hackers, can silently compromise hundreds of millions of iOS devices running older operating system versions through infected websites.
Information security
fromWIRED
4 weeks agoHundreds of Millions of iPhones Can Be Hacked With a New Tool Found in the Wild
A sophisticated iPhone hacking technique called DarkSword enables attackers to silently compromise iOS devices through infected websites, affecting hundreds of millions of users running older iOS versions.
fromMail Online
2 months agoWarning to all iPhone users over new spyware attack stealing data
The tech giant said the threat stems from the vast majority of users not updating to the latest version of their phone software, known as iOS 26. The patch includes advanced security upgrades for the latest vulnerabilities that hackers have allegedly been using in real-world attacks. Specifically, they've exploited sneaky flaws in the part of the iPhone that handles web browsing, called WebKit.
Apple
fromThe Hacker News
1 month agoApple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS
The vulnerability, tracked as CVE-2026-20643 (CVSS score: N/A), has been described as a cross-origin issue in WebKit's Navigation API that could be exploited to bypass the same-origin policy when processing maliciously crafted web content.
Information security
[ Load more ]