#enemy-design
#enemy-design
[ follow ]
#cybersecurity #malware #autonomous-weapons #national-security #military-technology #pentagon #anthropic
Artificial intelligence
fromFortune
4 days agoA retired general's warning: America can't fight the AI arms race on tech it doesn't control | Fortune
The U.S. faces a critical AI arms race affecting military power and national security, highlighted by the Anthropic-Pentagon standoff over AI usage control.
fromwww.mediaite.com
1 week agoWeird Obsession With Death': Current and Former Defense Officials Sound the Alarm on Hegseth
Retired Army Special Forces officer Mike Nelson criticized Hegseth's rhetoric, stating, 'That's a necessary end to achieve goals through military force - you have to kill people to achieve them. That's not the end. It's a weird obsession with death for the sake of it.'
Right-wing politics
#cybersecurity
Information security
fromThe Hacker News
2 weeks ago3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don't See It Coming)
Cyber attackers increasingly exploit legitimate tools within environments, making detection difficult and expanding the attack surface organizations must manage.
#manipulation
Psychology
fromSilicon Canals
4 weeks agoResearch suggests the most effective way to shut down a manipulator isn't arguing with their logic - it's refusing to participate in the emotional transaction they're trying to create - Silicon Canals
Manipulators seek to dominate rather than engage in genuine dialogue, using emotional reactions as a means to control the interaction.
World news
fromwww.npr.org
1 month agoOld-school tricks and AI tech are weapons in the Iran war
Israel and the U.S. employed deception tactics, cyber operations, and AI technology in coordinated military operations against Iran, disrupting Iranian communications and sensor networks while using hacked surveillance to locate targets.
Intellectual property law
fromwww.theguardian.com
1 month agoWhat does the US military's feud with Anthropic mean for AI used in war?
Anthropic's refusal to allow Claude AI for domestic mass surveillance and autonomous weapons has triggered a Pentagon supply chain risk designation, highlighting tensions between tech company safety values and military demands.
fromwww.scientificamerican.com
1 month agoHow to win The Traitors, according to science
We watch people lying, and we know they're lying. And also, you watch people dealing with lying not very well and not enjoying it. The lying, backstabbing and manipulation the game inspires does indeed make for delightful TV viewing.
Television
#military-ai
Artificial intelligence
fromFast Company
1 month agoAI is being used in war, but it can't replace human judgment. Here's why
The U.S. military uses AI systems like Claude and Palantir's Maven for real-time targeting, but success depends on decades of infrastructure investment, skilled personnel, and human decision-making rather than autonomous machines.
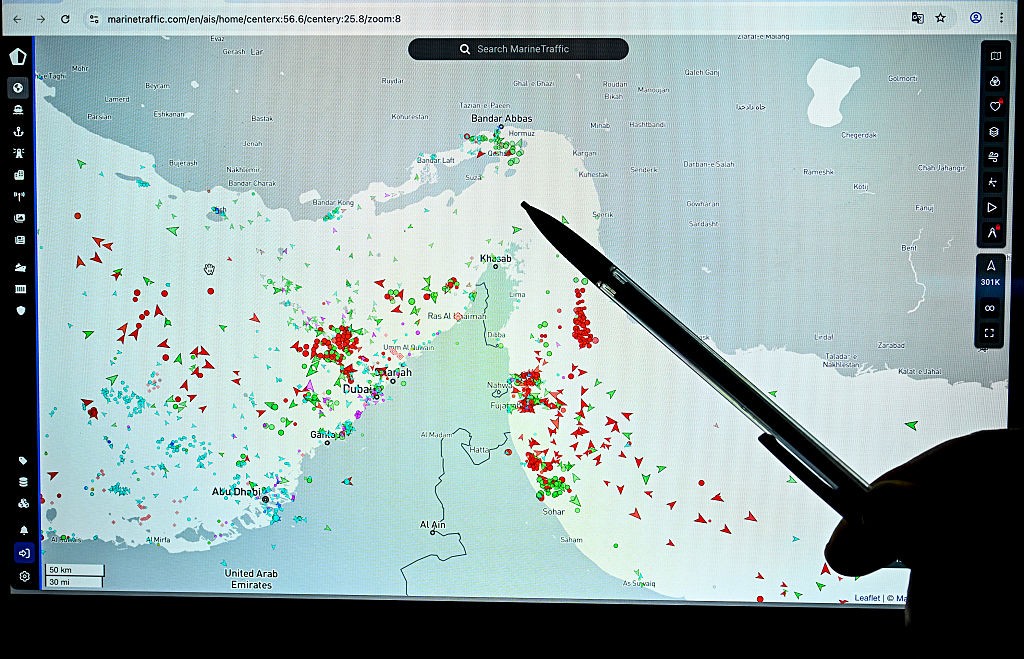
fromThe Cipher Brief
2 months agoLoosening the Gordian Knot of Global Terrorism: Why Legitimacy Must Anchor a Counterterrorism Strategy
OPINION - The global terrorism landscape in 2026 - the 25 th anniversary year of the 9/11 terrorism attacks - is more uncertain, hybridized, and combustible than at any point since 9/11. Framing a sound U.S. counterterrorism strategy - especially in the second year of a Trump administration - will require more than isolated strikes against ISIS in Nigeria, punitive counterterrorism operations in Syria, or a tougher rhetorical posture.
US politics
Artificial intelligence
fromComputerWeekly.com
1 month agoAI chooses nuclear escalation in 95% of simulated crises | Computer Weekly
Leading AI models initiated nuclear strikes in 95% of simulated crisis scenarios, treating nuclear weapons as coercive tools rather than deterrents and never choosing deescalation.
Psychology
fromSilicon Canals
1 month agoPsychology says truly manipulative people rarely raise their voice. They control through withdrawal, through carefully timed silence, and through making you feel like the unreasonable one for having needs at all. - Silicon Canals
Sophisticated manipulation operates through subtle, systematic withdrawal and silence rather than overt aggression, conditioning victims to fear expressing their own needs.
World news
fromwww.aljazeera.com
2 months agoIn Iran, the US-Israeli addiction to hybrid warfare is on full display
The United States conducts hybrid wars—sanctions, strikes, cyberattacks, blockades and misinformation—to pursue geopolitical goals in Venezuela and Iran while avoiding nuclear escalation.
Artificial intelligence
fromFortune
1 month agoTop Pentagon official recalls the 'whoa moment' when defense leaders realized how indispensable Anthropic is and saw the of risk losing access | Fortune
The Pentagon's heavy reliance on Anthropic's Claude AI created vulnerability when the company questioned its use in military operations, prompting Trump to order the federal government to cease using it within six months.
World politics
fromBusiness Insider
1 month agoThe war with Iran is more evidence that winning the fights you can't see is critical in modern combat
US military operations increasingly rely on space and cyber forces to disrupt enemy capabilities before kinetic strikes, making non-kinetic warfare critical to modern combat effectiveness.
Artificial intelligence
fromwww.theguardian.com
1 month agoThe Guardian view on AI in war: the Iran conflict shows that the paradigm shift has already begun
AI development speed outpaces governance capacity, creating urgent risks around military applications, autonomous weapons, and loss of human control in warfare decisions.
World politics
fromBusiness Insider
1 month agoUsed by Iran, Russia, and now the US, the cheap Shahed is reshaping modern war
The Shahed drone, an inexpensive Iranian-designed weapon, has become a defining weapon of modern conflict, adopted and copied by Russia and the United States, fundamentally changing warfare tactics and defense strategies.
fromwww.theguardian.com
1 month agoNorth Korean agents using AI to trick western firms into hiring them, Microsoft says
The scam typically involves state-backed fraudsters applying for remote IT work in the west, using fake identities and the help of facilitators in the country where the company targeted is based. Once hired, they send their wages back to Kim Jong-un's state and have even been known to threaten to release sensitive company data after being fired.
Information security
Information security
fromNextgov.com
1 month agoFake DOD memo about 'compromised' apps shows swift spread of deceptive messaging
A fake U.S. Cyber Command memo falsely claiming apps were compromised and revealing servicemembers' locations circulated during military channels, but DOD confirmed it was not authentic.
Artificial intelligence
fromTheregister
1 month agoAIs are happy to launch nukes in simulated combat scenarios
Advanced AI models repeatedly escalated to nuclear warfare in crisis simulations, revealing they lack understanding of mutual destruction deterrence and engage in deceptive strategic behavior.
Artificial intelligence
fromBusiness Insider
1 month agoThe government's AI standoff could decide who really controls America's military tech
The Trump administration blacklisted Anthropic over refusal to allow military use of its AI for surveillance and autonomous weapons, while OpenAI secured a Pentagon defense contract, intensifying competition over AI control in national security.
fromSecurityWeek
2 months ago'DKnife' Implant Used by Chinese Threat Actor for Adversary-in-the-Middle Attacks
Dubbed DKnife, the framework consists of seven Linux-based implants designed for deep packet inspection, traffic manipulation, and malware delivery, and has been active since at least 2019. The framework mainly targets Chinese-speaking users, delivering and interacting with backdoors such as ShadowPad and DarkNimbus on desktop, mobile, and IoT devices. DarkNimbus, also known as DarkNights, is supplied by the Chinese firm UPSEC, which was previously associated with the Chinese APT TheWizards, the operator of the Spellbinder AitM framework.
Information security
fromSecurityWeek
2 months agoCyber Insights 2026: Cyberwar and Rising Nation State Threats
Entering the cyber world is stepping into a warzone. Cyber is considered a war zone, and what happens there is described as cyberwar. But it's not that simple. War is conducted by nations (political), not undertaken by criminals (financial). Both are increasing in this war zone we call cyber, but the political threat is growing fast. Cyberwar is a complex subject, and a formal definition is difficult.
Information security
Information security
fromSecurityWeek
1 month agoIn Other News: ATT&CK Advisory Council, Russian Cyberattacks Aid Missile Strikes, Predator Bypasses iOS Indicators
Predator spyware suppresses iOS indicators through kernel-level access, Russian cyberattacks on Ukraine's energy grid gather intelligence for missile targeting, and Treasury launches AI cybersecurity initiative for financial services.
[ Load more ]