#defensive-transformation
#defensive-transformation
[ follow ]
#cybersecurity #iran #ai #national-security #vulnerabilities #military-strategy #crisis-management #security
Russo-Ukrainian War
fromwww.businessinsider.com
10 hours agoUkraine's Patriot crews are breaking from the norm, fighting Russian threats with fewer missiles
Ukrainian soldiers are using fewer Patriot interceptors against Russian missiles due to strained stockpiles, launching only one per threat instead of the standard two to four.
#crisis-management
Mental health
fromSilicon Canals
7 hours agoThe person who thrives during a crisis and falls apart during ordinary weeks isn't broken. Their entire operating system was built for emergencies, and peace registers as a system error because they never learned what competence feels like without urgency underneath it. - Silicon Canals
Crisis-thrivers are often dysregulated, struggling with normalcy after emergencies, revealing a deeper issue with their nervous system's response to stress.
Europe news
fromwww.businessinsider.com
19 hours agoThe West is preparing for cheap drone attacks, but many businesses and civilians can only watch, not stop them
Civilian and corporate organizations struggle to counter small drone threats due to legal restrictions, leading to increased demand for drone detection devices.
fromwww.mediaite.com
4 days agoWeird Obsession With Death': Current and Former Defense Officials Sound the Alarm on Hegseth
Retired Army Special Forces officer Mike Nelson criticized Hegseth's rhetoric, stating, 'That's a necessary end to achieve goals through military force - you have to kill people to achieve them. That's not the end. It's a weird obsession with death for the sake of it.'
Right-wing politics
#ukraine
Russo-Ukrainian War
fromFortune
4 days agoUkraine will have the most important defense industrial base in the free world, former CIA chief predicts | Fortune
Ukraine is emerging as a leading military industrial complex, producing advanced unmanned systems and reinforcing its role as the arsenal of democracy.
fromwww.nytimes.com
1 month agoOpinion | If A.I. Is a Weapon, Who Should Control It?
The current collision between the Department of Defense and Anthropic over whether Anthropic's A.I. models should be bound by ethical constraints or made available for all uses the Pentagon might have in mind raises significant concerns about the future of AI governance.
Right-wing politics
fromwww.businessinsider.com
14 hours agoWe're in a new era of heightened CEO safety measures, security pros say
This attack is just shedding light on the fact that you're even more vulnerable outside of the office, said Don Aviv, CEO of Interfor International, a security consultancy.
Information security
#cybersecurity-strategy
US politics
fromNextgov.com
1 month agoTrump's new cyber strategy details more offensive response to cyber threats
The White House released a national cybersecurity strategy prioritizing direct adversarial response, critical infrastructure protection, and offensive cyber capabilities alongside defensive measures.
Information security
fromSecurityWeek
1 month agoUS Cyber Strategy Targets Adversaries, Critical Infrastructure, and Emerging Technologies
Trump administration releases comprehensive cyber strategy emphasizing government-private sector coordination, deterrence, regulatory reform, and investment in AI and quantum technologies to strengthen national cybersecurity.
US politics
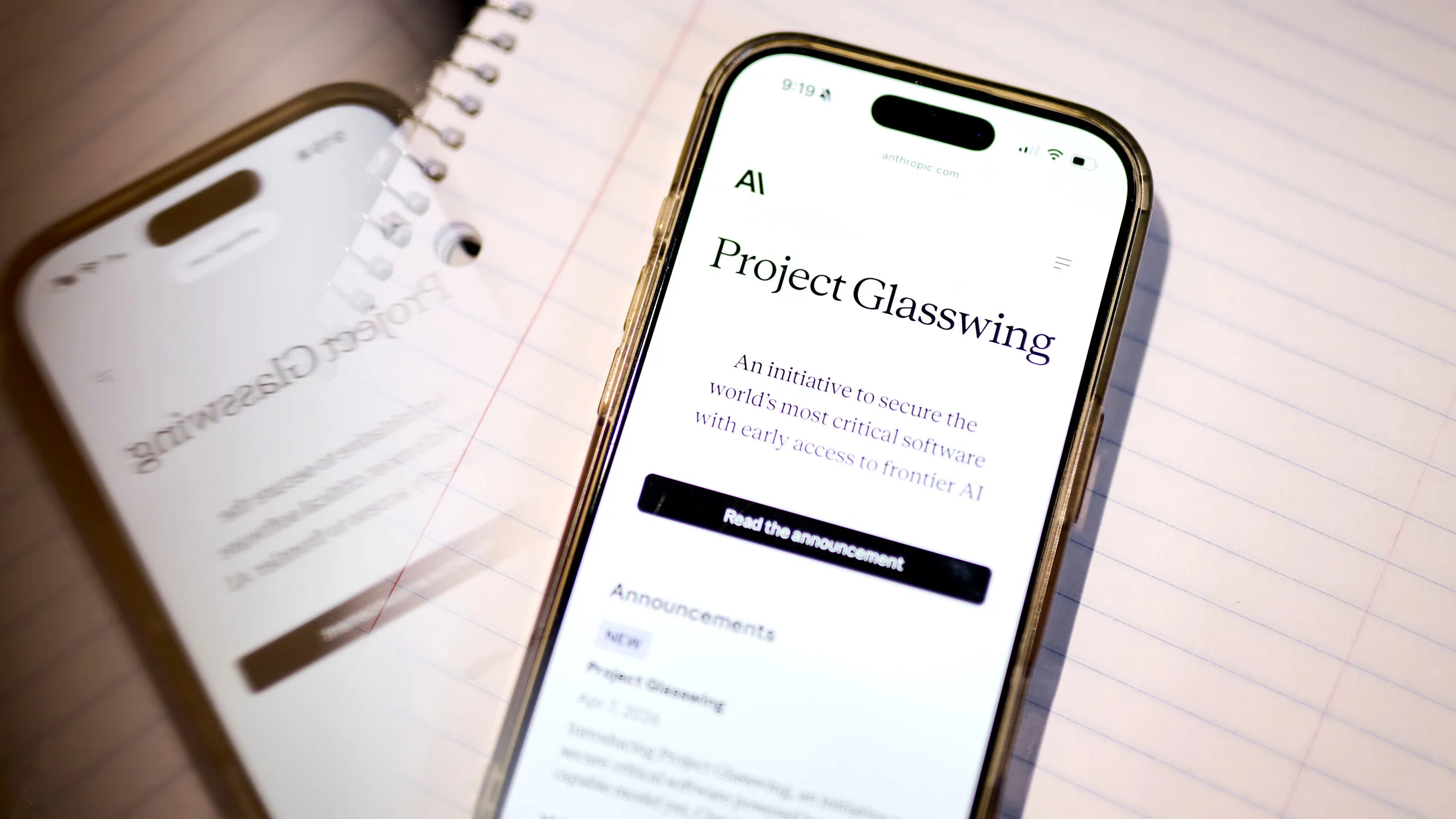
fromFortune
1 month agoPentagon officially defines Anthropic as 'supply chain risk' | Fortune
The Trump administration designated Anthropic as a supply chain risk, forcing government contractors to stop using Claude AI due to national security concerns over surveillance and autonomous weapons capabilities.
fromSecurityWeek
4 days agoMITRE Releases Fight Fraud Framework
"These incidents involve the intentional use of deceptive or illegal practices to fraudulently obtain money, assets, or information from individuals or institutions, and include actions carried out over cyber channels."
Information security
Venture
fromThe Cipher Brief
1 month agoWhat the Latest Policy and Tech Shifts Mean for National Security
Counter-Unmanned Aerial Systems require integrated, multi-layered defense architectures combining non-kinetic and kinetic responses rather than isolated legacy technologies, as modern autonomous drones render traditional electronic warfare ineffective.
fromSecuritymagazine
2 months agoThe New Battleground of Cybersecurity
I've always had what I would consider a hacker mindset, a curiosity to take things apart, understand them, and use that knowledge to solve problems. That mindset took me on a circuitous route into the cybersecurity industry; after being kicked out of high school for hacking computer systems, I worked a range of jobs, managing office supply companies by day and cracking Wi-Fi networks by night until I started a Digital Forensics degree which led me to the world of security research.
Science
fromNextgov.com
1 month agoUS cyber responses will be 'linked to adversary actions' and involve industry coordination, official says
Future U.S. government responses in cyberspace will be "linked to adversary actions" and will involve coordination between the private sector and smaller governments, a top White House official said Thursday. The dynamic, which will be codified in a forthcoming national cyber strategy, is meant to make clear that foreign adversaries' actions that target U.S. networks have consequences, according to Alexandra Seymour, who serves as the principal deputy assistant national cyber director for policy in the Office of the National Cyber Director.
US politics
fromThe Atlantic
2 months agoWhatever This Is, It Is Not Strategy
But logistical consistency, like coherence and gravitas, does not characterize the new NDS. It is a document that supposedly nests within the National Security Strategy, explaining at greater length the implications of overall policy for the armed forces. The 2026 version does not do that. Rather, it restates some of the basic priorities of the Trump administration but for the most part confines itself to flattery of the president, insults, and bombast.
US politics
Information security
fromSecuritymagazine
1 month agoSecurity Leaders Discuss Trump's Cyber Strategy for America
The Trump Administration released a cyber strategy with six pillars addressing adversary capacity, regulation, federal and critical infrastructure security, emerging technology innovation, and workforce development.
Information security
fromSecuritymagazine
1 month agoThe Great Security Culture Shift: Building a Proactive Defense in an Era of Advanced Threats and Social Engineering
Hackers exploit DLL side-loading on trusted platforms like LinkedIn to deliver malware through seemingly legitimate file attachments, bypassing traditional security defenses and compromising entire corporate networks.
fromSecurityWeek
2 months agoCyber Insights 2026: Cyberwar and Rising Nation State Threats
Entering the cyber world is stepping into a warzone. Cyber is considered a war zone, and what happens there is described as cyberwar. But it's not that simple. War is conducted by nations (political), not undertaken by criminals (financial). Both are increasing in this war zone we call cyber, but the political threat is growing fast. Cyberwar is a complex subject, and a formal definition is difficult.
Information security
[ Load more ]